When surfing the web, some end users have viewed a popup concept declaring Your computer has been compromised or hacked. Distinct consumers have seen this concept on different browsers, together with Chrome, Firefox, Edge, and so forth. After acquiring this warning concept, the impacted consumers scanned their computers with the antivirus put in on their units but the antivirus did not obtain any threat. If the antivirus menace report is clear, what does this information mean? Is this message genuine or faux? In this report, we will see what the Your laptop or computer has been compromised or hacked message implies and what you really should do if you see this message on your laptop or computer.

Your pc has been compromised or hacked message
In accordance to the suggestions of the impacted end users, their website browser refuses to shut following they get the popup information. Also, a call range is displayed alongside with the warning information. When they contacted that selection, the assistance human being requested them for some money to repair the difficulty. On the other hand, some customers have also reported that soon after going to a specific website web site, as a substitute of the warning popup concept, they listened to a voice stating “Your Laptop is hacked.”
Some consumers were also instructed to give accessibility to their computer systems in order to resolve the concern. This is a spam and deceptive message. You need to overlook it if not, you will come to be the prey of hackers. Moreover, if you grant obtain to your computer to the man or woman on the get in touch with, he/she could steal the info stored on your laptop that might consist of sensitive information and facts.
This kind of kinds of warning messages ordinarily screen possibly a contact amount or a website link. We recommend you do not click on the website link shown in these forms of warning messages. If you do so, a virus or malware may possibly enter your program and may perhaps start off sending your data to the hackers. Or, clicking on that link may perhaps install a system on your technique. That application may possibly have a suspicious code. Such forms of destructive plans are designed to improve the registry keys on a user’s pc.
If you see a Your computer has been compromised or hacked warning concept though browsing the world wide web, you must acquire the following ways promptly in get to protect your laptop or computer from malware or virus infection:
- Disconnect your Net relationship
- Near your net browser
- Scan your process with antimalware
- Update your web browser
- Eliminate unwanted extensions
- Delete your browser cache or reset your browser
- Uninstall the recently mounted plans
- Operate SFC and DISM scans
Under, we have explained all these techniques in depth.
1] Disconnect your World wide web link
Right away disconnect your Web link 1st.
2] Near your world wide web browser
The upcoming issue that you should really do is to shut your world-wide-web browser. But according to the users, the popup information may well prevent you from closing the net browser. If such a factor transpires to you, abide by the underneath-outlined methods to shut your net browser:
- Push the Ctrl + Shift + Esc keys to start the Job Manager.
- When the Endeavor Supervisor appears on your display, pick the Processes tab.
- You will see your world-wide-web browser less than the Applications section. Proper-simply click on your internet browser and pick out Conclude Undertaking.
If the higher than system fails, pressure shut down your laptop or computer by pressing and holding the electrical power button and then switch it on.
3] Scan your process with antimalware
If you have clicked on the website link delivered in the warning message or if you have granted access to your computer to the particular person on connect with, there is a solid risk that your laptop or computer has been contaminated by a virus. Run a complete program antivirus scan.
Browse: How do you tell if your computer system has a virus?
4] Update your world wide web browser

Start your world-wide-web browser and near all the opened tabs if any.
Now update your website browser. It is encouraged to usually use the most recent edition of the software in get to steer clear of glitches. If you use the most recent variation of the net browser, the probabilities of receiving a virus or malware assault grow to be significantly less.
Go through: On the internet Fraud in Cyber criminal offense: Prevention, Detection, Restoration
5] Clear away undesirable extensions

Now, the future action is to remove undesirable extensions from your web browser. Extensions make our perform much easier on a website browser. Occasionally, extensions lead to troubles. If you have clicked on the hyperlink displayed in the warning message, it is possible that an extension is installed on your browser with no your information. Therefore, it is essential to check if there is any unwanted extension put in on your browser. If you locate any undesired extension or an extension that is set up on your net browser devoid of your information, take away it promptly.
Study: Malware Removing Information & Applications for Rookies.
6] Delete your browser cache or reset your browser
You ought to also delete your browsing heritage, which includes the cookie and cache data. Push the Ctrl + Shift + Delete keys to open up the Very clear Browsing Knowledge window in your world-wide-web browser. This shortcut will work with most website browsers. When the Obvious Searching Facts window seems, decide on cookies, cache, and searching record. In the time vary, decide on All Time. If you want to delete your saved passwords, you can also do that.
Alternatively, you could want to contemplate resetting your browser to default condition to be extremely risk-free.The methods to reset some well-liked website browsers are defined below:
- To reset or refresh Mozilla Firefox, open up its configurations and go to “Aid > Troubleshooting Details.” Now, click on the Refresh Firefox button.
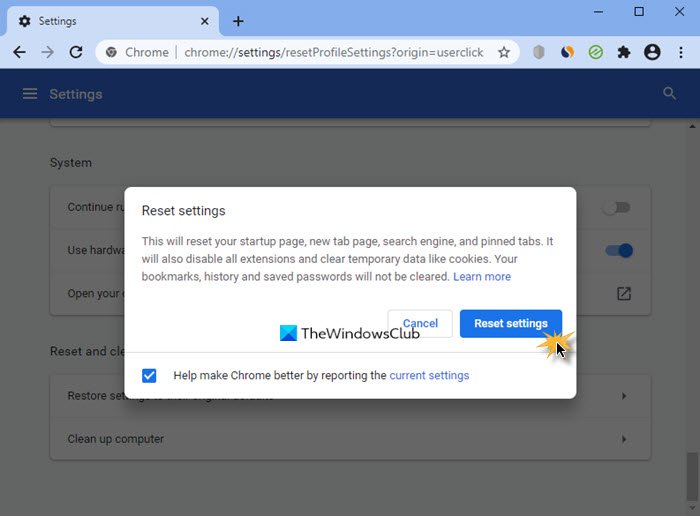
- To reset Google Chrome, open up its settings and go to Highly developed Options. Now, click on on the Restore configurations to their initial defaults button.
- To reset Microsoft Edge, open up its options and then click on on the Reset Configurations choice on the left pane.
7] Uninstall the a short while ago set up courses
If you have identified as the scammers or clicked on the link exhibited in the warning concept, the scammers might have put in a plan on your method. Open the Applications & Attributes page in Home windows 11/10 Settings and see if there is any lately put in system. If of course, uninstall it instantly. The subsequent methods will guidebook you on how to do that.

- Open Home windows 11/10 Options.
- Go to “Applications > Applications & Features.”
- Form all the set up plans by date. For this, find Date installed in the Type by drop-down.
- See if there is any program that is put in devoid of your awareness. If of course, uninstall it.
8] Run SFC and DISM scans
It is also doable that some of your method picture documents are ruined due to malware or virus infection. To examine this, run an SFC scan. SFC stands for Method File Checker. It is an automatic tool created by Microsoft that checks for ruined or corrupted technique graphic files and repairs them (if feasible).
We also propose you operate a DISM scan on your method. The DISM or Deployment Impression Servicing and Administration is a command-line tool. Like SFC, it also repairs the corrupted or harmed system graphic information. It is ordinarily utilized when SFC fails to maintenance the program impression data files.
Examine: What to do after a Ransomware attack on your Windows computer?
What does it mean if your computer is compromised?
A compromised personal computer is a pc, the confidentiality of which is adversely impacted, possibly intentionally or unintentionally. The phrase Compromised pc is usually utilized for hacked personal computers. There are a lot of methods by which hackers can hack your process. The most popular way is the phishing attempt. The phishing attempts are ordinarily performed by sending an e mail to the user with some suspicious inbound links. When a user clicks on these back links, he will be redirected to the site that appears to be exactly the exact as the official internet site. These internet websites trick users and they enter their private data whilst signing in. In this way, hackers steal the private information and facts of the users.
Although surfing the web via your net browser, some of you could possibly have observed the messages very similar to the subsequent kinds soon after viewing some certain web-sites:
- Your computer might be at hazard. Run a cost-free antivirus scan to secure your personal computer.
- Virus detected. Run a no cost antivirus scan to take out the virus from your computer system.
Such kinds of websites are destructive internet websites. Clicking on any of the one-way links on these types of websites installs malware on the user’s computer. Immediately after the malware is set up, a destructive code is executed on his/her computer system and the hacker is able to steal the information from the infected personal computer. Some malware are also capable of transforming the registry keys on a Home windows computer.
Idea: Secure on your own, steer clear of online ripoffs and know when to trust a web-site!
Does Microsoft phone you about your computer staying hacked?
Keep in thoughts that neither Microsoft nor its companions contact you for your pc safety problems. You will need to learn how to determine cons that fraudulently use the Microsoft identify. The motive of these calls is to steal the confidential facts from the user’s computer so that they could use it for blackmailing applications. The person on contact could also question to obtain your personal computer by installing a unique software package. If you grant him/her obtain to your computer, he/she could execute a destructive code on your process or wholly lock your laptop or computer. Soon after that, the hacker will inquire you for a sure quantity of cash to unlock your laptop.
Hope this will help.
Examine following: Command and Management Cyberattacks: How to Recognize and Avoid them?